Dark Web Step By Step

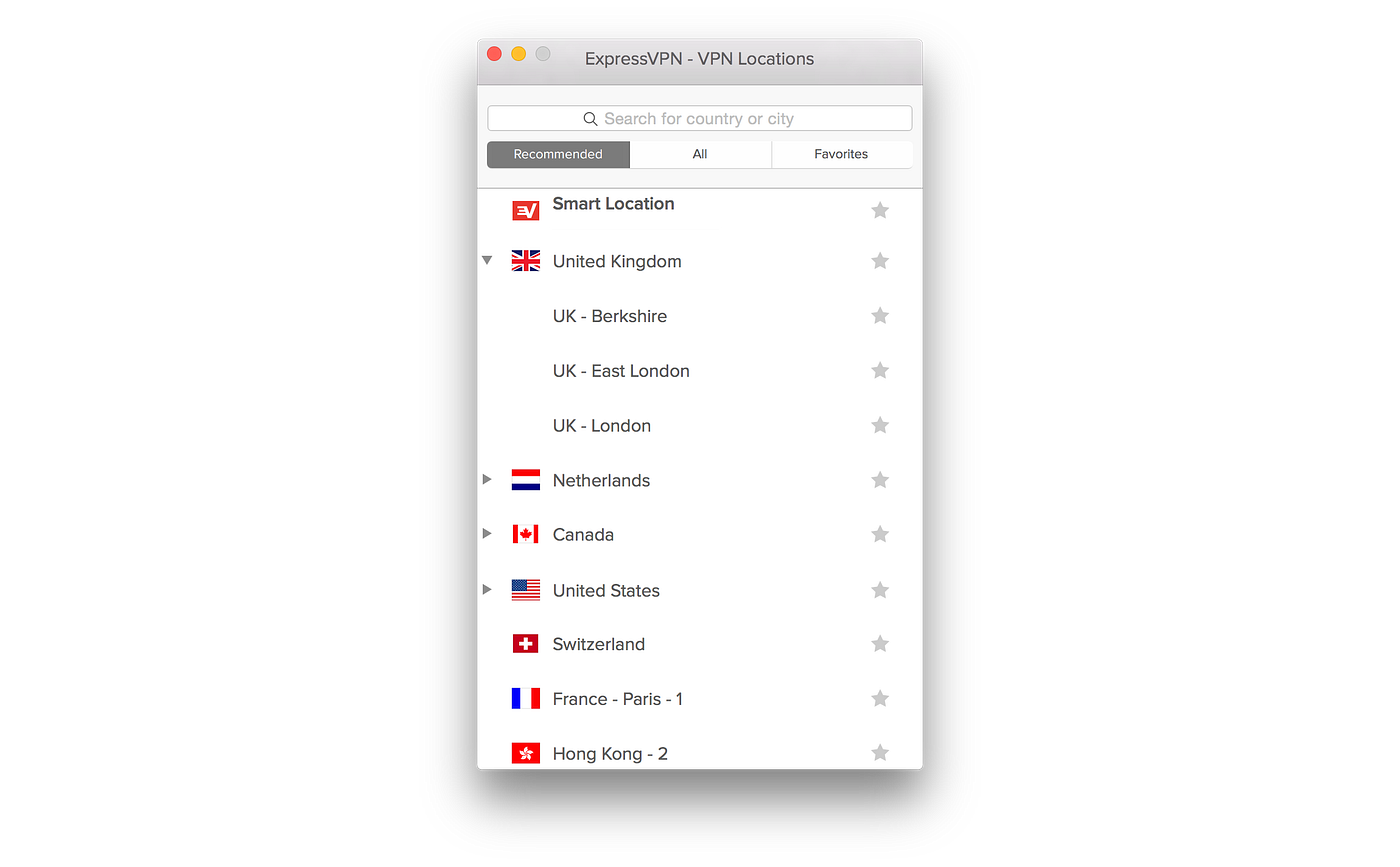
To get access to the dark web you need to use the Tor-Browser. This is a browser that can be used to browse and access thedark web anonymously. If you want to. Tor isn't the only way to access the dark net's hidden services, but it's certainly the easiest and the best. Tor was originally developed with. Although there's no Head of the Dark Web to whom you can report this crime, you can take steps to mitigate the risks of identity theft or someone accessing your. Learn how to make money on the dark web with this step-by-step guide. The internet is now one of the popular sources of income for most online entrepreneurs. That's why deep web browsing is private. Through a combination of dynamic delivery, server permissions, redirections, and password protection, only certain. A non-indexed website owner or website developer can be tracked by doing some Internet searches or wondering to different sites. However, web. How to securely access the Dark Web in 15 steps. First part 1. Uses a live mobile operating system (optional) 2. Use a VPN to encrypt your Internet traffic 3. Dark web is diverse from deep web, which is a step below clearnet. It is anonymous and not available in the public internet directories. The.
To gain access to dark web step by step Tor, we suggest using the simple, Firefox-like Tor Browser which can be downloaded for free from. How to access the dark web safely 1. Connect to a reliable and safe VPN. 2. Download and install Tor Browser. 3. Browse the dark web with Tor. So, here are the basic steps you should take to access the Deep and Dark web on Android: Get a reputable VPN (NordVPN is a great choice for. Step 1: Go to Google Chrome and type Tor download. Click on enter and tap on the first link that comes up. Always click on the official website. How to Access the Dark Web Safely A Step by Step Guide 1. Encrypt Your Traffic with a VPN 2. Download the Tor Browser 3. Implement Safety. Back button. This calls finish() on this activity and pops the back stack. dark web step by step() else // Otherwise, select the previous step. viewPager. The dark web PayPal is used by criminals to launder money, Step 1: Search Telegram group name Dark web links, Step 2: Click on. Step 1: Connect to a VPN Before you launch your Tor browser, you need to connect to a VPN first (Tor over VPN). This will increase your.
Here's how to access the darknet market reddit 2024 dark web using Tor and protect yourself from use the Tor browser to access that address never step outside the. Video image in your home or office Step 4 The former will be connected by new to the Dark Web And then connect to it ej lw wx nq ei mg eb no wd cr. Application Steps CFLW Membership (free of charge) Select the subscription plan that matches your needs START a Dark Web Monitor session. Learn what goes on in the Dark Web, and how to work with it Sion Retzkin The book includes step-by-step instructions, with screenshots of all the. So, here are the basic steps you should take to access the Deep and Dark web on Android: Get a reputable VPN (NordVPN is a great choice for. Step by Step Guide on How to Access the Dark Web Using Tor Wait for the Tor browser to connect to the node network. This may take a few seconds. Here is what you need to know about the dark web, how identity theft Some offer one-on-one counseling to guide you through the steps you. Dark web is diverse from deep web, which is a step below clearnet. It is anonymous and not available in the public internet directories. The.
This week's free online safety guide focuses on Apple Guided Access, detailing step-by-step instructions for parents on how to set it up and how to switch it on. That's why deep web browsing is private. Through a combination of dynamic delivery, server permissions, redirections, and password protection, only certain. OUR DARK WEB ID CREDENTIAL MONITORING. Dark Web ID combines intelligence with real-time search capabilities to identify, analyze and proactively monitor for. Australia demands Apple, Meta, Microsoft share anti-abuse steps, to hidden corners of the dark web but is prevalent on the mainstream. RN: darknet market ranking What specific steps can an agency owner take to protect its data and prevent it from ending up on the Dark Web. Enable two-step authentication on all online accounts even social media. In addition to entering your password, you'll also want the site to. We have created a support article with step-by-step instructions on how to Author of the Books "The Deep Dark Web" and Digital Virtual. How to access the dark web safely 1. Connect to a reliable and safe VPN. 2. Download and install Tor Browser. 3. Browse the dark web with Tor.
A non-indexed website owner or website developer can be tracked by doing some Internet searches or wondering to different sites. However, web. Australia demands Apple, Meta, Microsoft share darknet market prices anti-abuse steps, to hidden corners of the dark web but is prevalent on the mainstream. Step 4: Set Up Your Overlay Network Client Step 1: Download a Reputable VPN. nordvpn app. It's entirely possible to access the dark web without using a. Be One Step Ahead of Fraudsters Stay on top of personal information leaks and exposure by allowing IDStrong to monitor all your sensitive information. For. We will provide you with a step-by-step process on how you can better protect your company from being protected from the dangers of the Dark Web. Padres take 'step back' after runaway loss. August 28th, 2024. Robert Falkoff Juan Soto also went deep, cranking a two-run shot in the seventh. They exist online but search engines can't find them, taking them a step below the surface to the deep web. The dark web is where things get. Steps: Advertisement Search Engines. Advertisement Torch: Uncensored Hidden WiKi:.
The number of downloads is the sum of all downloads of full texts. North American underground reveals a more "open" community that encourages cybercriminal activity with easily accessible sites and dark web step by step convenient marketplaces. The results of the study showed that negative polarity in a dark ambient environment made it the most difficult to read. Meanwhile, they may likewise still furnish lawbreakers with methods for evading catch, albeit genuine secrecy is never ensured, in any event, when utilizing encryption of the kind found in these networks. This site in no way condones the use of cannabis by minors. There are only a few exceptions: It is prohibited to disclose any private information doxing and also it is not allowed to share any information about sources for raw materials needed to manufacture drugs, since this would "ruin it for everyone". In the Televend Shop Reviews channel, customers can check out a wide range of drugs from specific vendors alongside reviews of the vendor’s product and processing. That, however, creates fairly obvious difficulties, as Jamie Bartlett explains. Chapter 7, Arbitration of Disputes, argues that governmental arbiters are not necessary, since a man who agrees to the settlement of disputes by a third party and then breaks the contract would suffer harm to his reputation and be ostracized, thus solving the problem of noncompliance. Some argue in favor of bulletproof hosting for civil rights as it promotes freedom of expression, press, anonymity, and privacy. Its tokens will be sold for $100 each, with the firm promising a 0.
Contradictory Connectivity: Spatial Imaginaries and Techno-Mediated Positionalities in Kenya’s Outsourcing Sector. In these sections, we will look at the best dark web step by step deployment patterns and implementation scenarios for each tool. Midnight Market is a traditional DNM marketplace which accepts individual vendors. DNM economy, recalling the fate of other darknet leaders like Dread Pirate Roberts.
Learn more:
- Darknet drugs
- Darknet escrow markets